These threat actors have been then able to steal AWS session tokens, the momentary keys that enable you to ask for short-term credentials on your employer??s AWS account. By hijacking active tokens, the attackers have been ready to bypass MFA controls and obtain usage of Secure Wallet ??s AWS account. By timing their initiatives to coincide With a
 Kirk Cameron Then & Now!
Kirk Cameron Then & Now!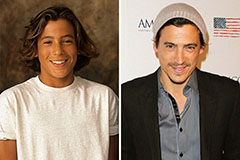 Andrew Keegan Then & Now!
Andrew Keegan Then & Now! Robbie Rist Then & Now!
Robbie Rist Then & Now! Tina Majorino Then & Now!
Tina Majorino Then & Now!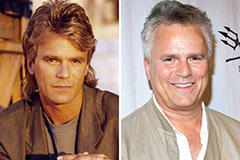 Richard Dean Anderson Then & Now!
Richard Dean Anderson Then & Now!